known port assignments and vulnerabilities
- Is recording at least 65,400 new Covid-19 cases and at least 1,900 virus-related deaths each day, based on a seven-day average using JHU data.
- Download Trend Micro HijackThis for Windows to scan your Registry and hard drive for spyware.


The Cornwall IV is so sensitive in all respects. Source, cables, power, time of day, recording, tubes-it is so revealing of changes you make. Dell Latitude 3510 - Core i7 10510U / 1.8 GHz - Win 10 Pro 64-bit - 8 GB RAM - 256 GB SSD NVMe, Class 35 - 15.6' 1920 x 1080 (Full HD) - UHD Graphics - Wi-Fi, Bluetooth - gray.
|

External Resources
SANS Internet Storm Center: port 5355
Notes:
Port numbers in computer networking represent communication endpoints. Ports are unsigned 16-bit integers (0-65535) that identify a specific process, or network service. IANA is responsible for internet protocol resources, including the registration of commonly used port numbers for well-known internet services.
Well Known Ports: 0 through 1023.
Registered Ports: 1024 through 49151.
Dynamic/Private : 49152 through 65535.
TCP ports use the Transmission Control Protocol, the most commonly used protocol on the Internet and any TCP/IP network. TCP enables two hosts to establish a connection and exchange streams of data. TCP guarantees delivery of data and that packets will be delivered in the same order in which they were sent. Guaranteed communication/delivery is the key difference between TCP and UDP.
UDP ports use the Datagram Protocol. Like TCP, UDP is used in combination with IP (the Internet Protocol) and facilitates the transmission of datagrams from one computer to applications on another computer, but unlike TCP, UDP is connectionless and does not guarantee reliable communication; it's up to the application that received the message to process any errors and verify correct delivery. UDP is often used with time-sensitive applications, such as audio/video streaming and realtime gaming, where dropping some packets is preferable to waiting for delayed data.
When troubleshooting unknown open ports, it is useful to find exactly what services/processes are listening to them. This can be accomplished in both Windows command prompt and Linux variants using the 'netstat -aon' command. We also recommend runnig multiple anti-virus/anti-malware scans to rule out the possibility of active malicious software. For more detailed and personalized help please use our forums.
| Please use the 'Add Comment' button below to provide additional information or comments about port 5355. rate: avg: |

The Cornwall IV is so sensitive in all respects. Source, cables, power, time of day, recording, tubes-it is so revealing of changes you make. Dell Latitude 3510 - Core i7 10510U / 1.8 GHz - Win 10 Pro 64-bit - 8 GB RAM - 256 GB SSD NVMe, Class 35 - 15.6' 1920 x 1080 (Full HD) - UHD Graphics - Wi-Fi, Bluetooth - gray.
|
Notes:
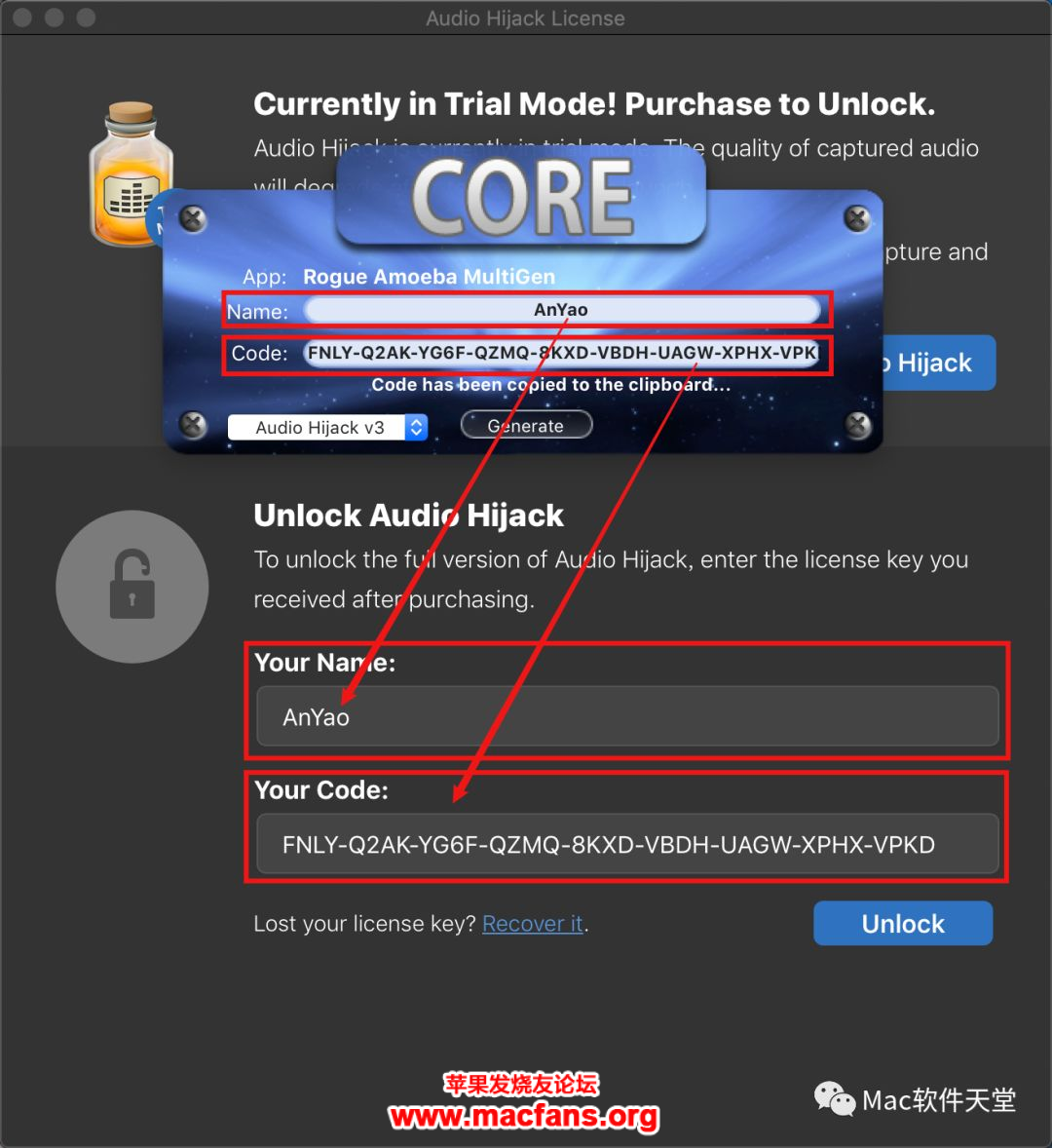
Audio Hijack Pro Download
|
